By the time a company calls us about executive protection, something inside the organization has usually broken or come close to it. Here’s what we keep seeing, and what corporate decision-makers can do about it.
When a company reaches out to Silent Professionals about executive protection, we already know something about the shape of the conversation before it starts. By the time someone contacts us, something internal has usually broken, or come close enough that someone got scared.
Sometimes it is a board member who finally asked a question nobody had a clean answer to. Are we actually covered? Sometimes it is a public-facing executive who started receiving credible threats. Sometimes it is an incident. A former employee showing up in the lobby. A doxxing campaign that reaches the principal’s residential street. A protest at a facility that was not supposed to know where the principal lives. The trigger is different every time. The pattern underneath is the same.
Once we are in those conversations, we see the same internal gaps over and over. They are worth talking about, because most of them are fixable, but only if the right people are at the table.
Who Is Actually in the Room
In most corporations we work with, the security function is owned by someone whose career was built somewhere else. Compliance. Investigations. Facilities. HR. They are smart, capable professionals. They got promoted into a security role because the org chart needed an owner, not because they have direct, operational experience with physical threats against principals.
That promotion path produces a few predictable problems.
First, the security leader is often the only voice in the room.
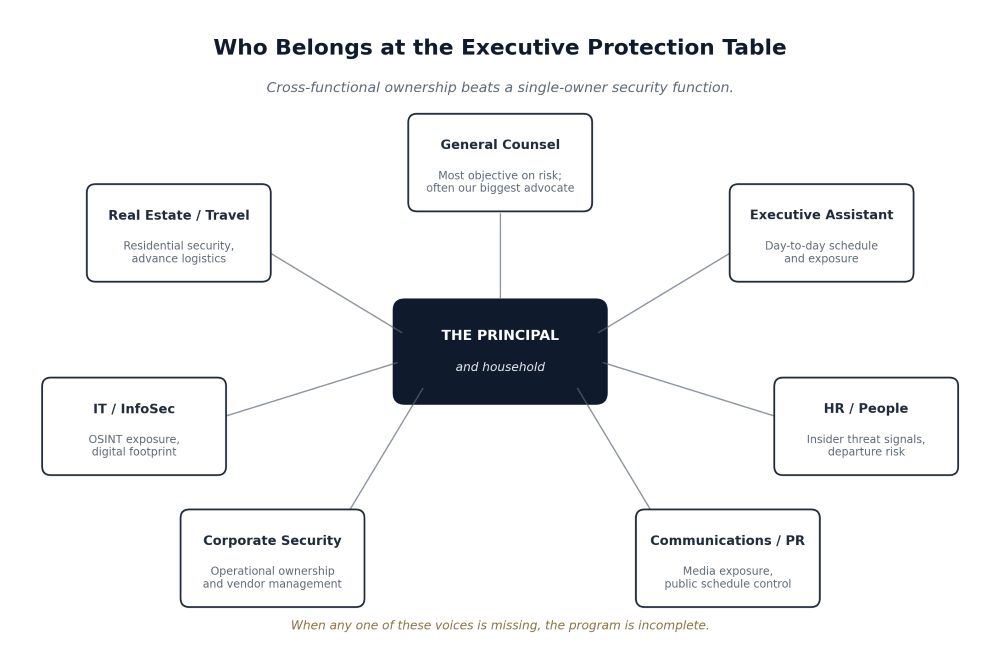
When we get brought in, we ask who else needs to weigh in. General Counsel. HR. IT and InfoSec. The principal’s executive assistant. Communications. Real estate. Travel. The answer is usually some version of “this is a security decision, so it sits with corporate security.” Almost always, it does not. Executive protection cuts across privacy law, employment law, online exposure, residential and travel logistics, brand risk, and insider threat intelligence. Keeping that conversation inside one office, especially an office that does not have direct operational experience, is how executive protection programs end up shaped around whatever that one person is comfortable with.
Second, that same security leader has to defend a budget to a CFO who has never seen what a serious threat actually looks like.
Without operational language and current threat data, they lose that conversation. The result is a program built on what the company is willing to pay for, not what the principal’s threat profile actually requires.
Third (and this is the one that kills the most programs) the corporate security director is frequently the biggest obstacle to the program getting better.
When more capable outside talent enters the conversation, the person whose job it is to own security can feel threatened by it. The response is gatekeeping. Slow-walking. Narrowing the scope of what the outside team is asked to do. Filtering information from reaching the principal or the board. We have seen this pattern in companies of every size, and in our experience it is almost always the deciding factor in whether the program improves or stays broken.
Of all the voices in those conversations, the one we end up working with most productively is almost always General Counsel. That sounds counterintuitive at first. It stops sounding counterintuitive after a few of these conversations. Attorneys assess risk for a living. They do it without an ego stake in the security budget or in who gets hired. They have visibility into exposures the security function does not always see, including litigation, employment disputes, and threats that have already produced demand letters or restraining orders. In our experience, GCs have consistently been the most objective voice in the room and frequently end up being our biggest internal advocates.
Credentials Are Not Capability
There is a second issue we run into constantly, and it deserves to be said plainly. A degree or certification in security is not a substitute for capability against real-world threats.
We respect the academic side of the field. ASIS certifications, security management programs, and adjacent credentials matter — but only in that they create a shared vocabulary, they professionalize the function, and they signal seriousness. They do not, on their own, prepare anyone to assess and counter a determined adversary.
The 2024 killing of UnitedHealthcare CEO Brian Thompson made that point at the cost of a man’s life. The decisions that mattered in the lead up to that incident were not academic ones. Public schedule. Route discipline. Residential address exposure. Online targeting indicators. Those are operational decisions, and they require people who have lived in operational reality.
When we evaluate the people on the other side of the table from us, we are not asking what they studied. We are asking what they have actually done.
– Have they run protective advances in hostile environments?
– Have they handled a credible threat from the indicators stage to resolution?
– Do they read open source intelligence the way an adversary does, not the way a policy document tells them to?
– Do they understand that a principal’s spouse, children, executive assistant, and household staff make up the actual attack surface, not just the principal’s calendar?
If the person leading a corporate security program cannot answer those questions, they cannot meaningfully evaluate vendors, scope a program, or push back when something is wrong. They will buy from whoever fits the budget and will give them whatever they ask for without evaluating the threats.
The Current Threat Picture
The threat picture moves faster than most corporate programs can keep up with. Here’s a short, partial view of what we are seeing in the field today:
Online radicalization turning into real-world action
The same dynamic that produced the Thompson killing is showing up in healthcare, energy, technology, and financial services. A grievance ecosystem forms online, attaches to a face, and produces a small number of actors willing to act on it.
OSINT driven targeting
Property records, court filings, school directories, fitness app traces, and corporate disclosures combine into a precise picture of where a principal is and when. Adversaries do not have to guess anymore.
Insider and former insider threats
Disgruntled current and former employees are still the most common credible threat to most corporations. They know the building, the routine, and the people. They have rarely been threat modeled by the security program.
Stalking, especially against female executives and public-facing leaders
This category is consistently under resourced. The signals are usually present months before a physical incident. They are usually missed.
Activist targeting in contested industries
Energy, biotech, AI, defense, finance and healthcare are drawing organized attention that increasingly extends to executives’ homes. Residential security is no longer an optional line item.
Travel risk in markets that look stable on a map
Kidnap for ransom, extortion, and credible surveillance are present in markets that rarely make it into the corporate risk register because the company “operates there safely.”
None of this is exotic. It is current. And almost none of it gets addressed by a program built around badging, lobby control, and incident reporting.
What Better Programs Have in Common
The companies that get this right tend to share a few traits.
- Threat assessment comes first. A real protective program starts with an honest read on who would target this principal, why, with what resources, and through what vectors. Vendor and staffing decisions come after that, not before.
- The internal table is cross-functional from day one. The principal, General Counsel, HR, IT and InfoSec, the executive assistant, communications, and corporate security all have something to contribute. In our experience, General Counsel is usually the most useful partner because attorneys evaluate risk professionally and without an ego stake in the security function. Bring them in early.
- Vendors are partners, not panic hires. The companies that fare best build relationships with capable vendors before a crisis, run small engagements to test fit, and grow the relationship as trust builds. The companies that fare worst Google “executive protection [city]” the day after an incident.
- Operators get vetted as people, not as résumés. A lot of firms and individuals in this industry overstate or fabricate their backgrounds. “Classified” is not an answer. Legitimate military and law enforcement service can be verified. If a vendor cannot or will not let their people be vetted, that is the answer.
- The program is continuous. Threat profiles drift. Principals change roles, change addresses, attract different attention. A program that gets reviewed only after an incident is a program that is permanently behind.
A Word to the People Above Corporate Security
If you are a CEO, board member, General Counsel, or CHRO reading this, the single most useful thing you can do is stop treating executive protection as a line item your security director will figure out.
Ask three questions of your security leadership, and listen carefully to the answers.
- Who would target our principals, why, and through what vectors? Walk me through the current assessment.
- Who, internally, is at the table when we make protection decisions, and why those people?
- Of the people we have hired or contracted to protect our principals, who has actually operated against the threat we are buying coverage for?
If those questions get answered with confidence, specifics, and current information, your program is probably in good shape. If they get answered with credentials, certifications, vendor names, and reassurance, you have learned something important.
The Call We Would Rather Get
The call we want is the one that comes before the incident. From a company that is taking its threat picture seriously, has the right people in the room, and wants operationally proven talent vetted to a real standard. That call is becoming more common.
But the calls we still get most often come after something has already gone wrong, or come close enough to wrong to scare a board. Those calls are recoverable. We have helped a lot of companies rebuild from that point. It is just a more expensive, more painful, and slower path than the one we would rather see them on.
If you are protecting principals against real threats, you need people who have actually operated against those threats. Anything less than that is theater.
Silent Professionals is a vetted-only network of combat veterans and operationally proven security personnel for executive protection, residential security, advance work, and high-threat environments. We work with corporate clients who are taking their threat picture seriously and want talent that has actually operated against it.
